Lesson 1
An Introduction to Your Nanodegree Program
Welcome! We're so glad you're here. Join us in learning a bit more about what to expect and ways to succeed.

Nanodegree Program
You’ll master the foundational skills necessary to become a Security Engineer. This program will focus on how to protect a company’s computer systems, networks, applications and infrastructure.
You’ll master the foundational skills necessary to become a Security Engineer. This program will focus on how to protect a company’s computer systems, networks, applications and infrastructure.
Intermediate
4 months
Real-world Projects
Completion Certificate
Last Updated December 1, 2023
Course 1 • 45 minutes
Lesson 1
Welcome! We're so glad you're here. Join us in learning a bit more about what to expect and ways to succeed.
Lesson 2
You are starting a challenging but rewarding journey! Take 5 minutes to read how to get help with projects and content.
Course 2 • 4 weeks
This course introduces the fundamental concepts and practices of security engineering including basic security principles and practical applications of cryptography. You will also learn strategies to implement risk evaluation, security review, and audit.
Lesson 1
In this lesson, you'll be introduced to the course and what to expect!
Lesson 2
In this lesson, you'll be introduced to Security Engineering and different facets of security.
Lesson 3
In this lesson, you'll be introduced to the CIA triad, Authorization, Authentication, Non-Repudiation, and the Principles of Secure Design.
Lesson 4
In this lesson, you'll learn about encryption, hashing, and their uses in modern security.
Lesson 5
In this lesson, you'll learn how to evaluate risks and begin suggesting mitigations and creating models.
Lesson 6
In this lesson, you'll learn the how a Security Engineer interacts with the review and audit process.
Lesson 7 • Project
In this lesson, you'll work with a company to assess threats and suggest mitigations.
Course 3 • 4 weeks
In this course, you will learn about implementing authentication and authorization You will learn how to build and utilize tools that can alert you to system security breaches and you'll know how to effectively counter them.
Lesson 1
In this lesson, you'll be introduced to the course and what to expect!
Lesson 2
In this lesson, you will start learning about third party vulnerabilities and how to protect against them.
Lesson 3
In this lesson, you will learn about password management tools, securing remote access, and encryption.
Lesson 4
In this lesson, you will learn about access control, ownership and permissions, and creating rules and filters.
Lesson 5
In this lesson, you will learn about restricting access, access control, and memory attacks.
Lesson 6
In this lesson, you will learn about logging and monitoring.
Lesson 7 • Project
In this project, you will detect a threat, mitigate it, and harden a system in the aftermath of a nation-state cyber attack.
Course 4 • 4 weeks
In this course, you will be introduced to the industry best practices for security configurations and controls.
Lesson 1
This lesson introduces this course and the instructor to help set your learning path.
Lesson 2
In this lesson you'll set the foundation for good security assessment practices.
Lesson 3
In this lesson, you'll learn about access management to make sure your files and data are secure.
Lesson 4
In this lesson you'll learn how to monitor and detect issues inside your perimeter.
Lesson 5
In this lesson you'll learn about identity management.
Lesson 6
In this lesson you'll learn about the top security failures inside of a perimeter and how to mitigate them
Lesson 7 • Project
The project and its details for this course.

VP of Product Innovation
Dev has worked in the cybersecurity field for more than 10 years, and is now VP of Product Innovation at one of the top cybersecurity companies. His area of expertise is red team and exploit development, with a focus on active cybersecurity defense.

Principal Security Research Engineer, Splunk
Rod has over 15 years of experience in information technology and security. He has worked at Prolexic, Akamai, Caspida, and Splunk. He is the co-founder of HackMiami and the Pacific Hackers meetup and conferences.

Engineer/Consultant, Amazon Web Services
Abhinav is a cybersecurity researcher with nearly a decade of experience working for global leaders in security technology, financial institutions and as an independent consultant. He is the author of Metasploit Penetration Testing Cookbook and Instant Wireshark Starter, as well as many papers, articles, and blogs.

Head of Information Security, Clearwater Analytics
Taylor is an information security leader with over 10 years experience building a wide range of security programs. Taylor is currently head of information security for Clearwater Analytics. Previously he was a leader in application security at Adobe.
Average Rating: 4.7 Stars
32 Reviews
Combine technology training for employees with industry experts, mentors, and projects, for critical thinking that pushes innovation. Our proven upskilling system goes after success—relentlessly.
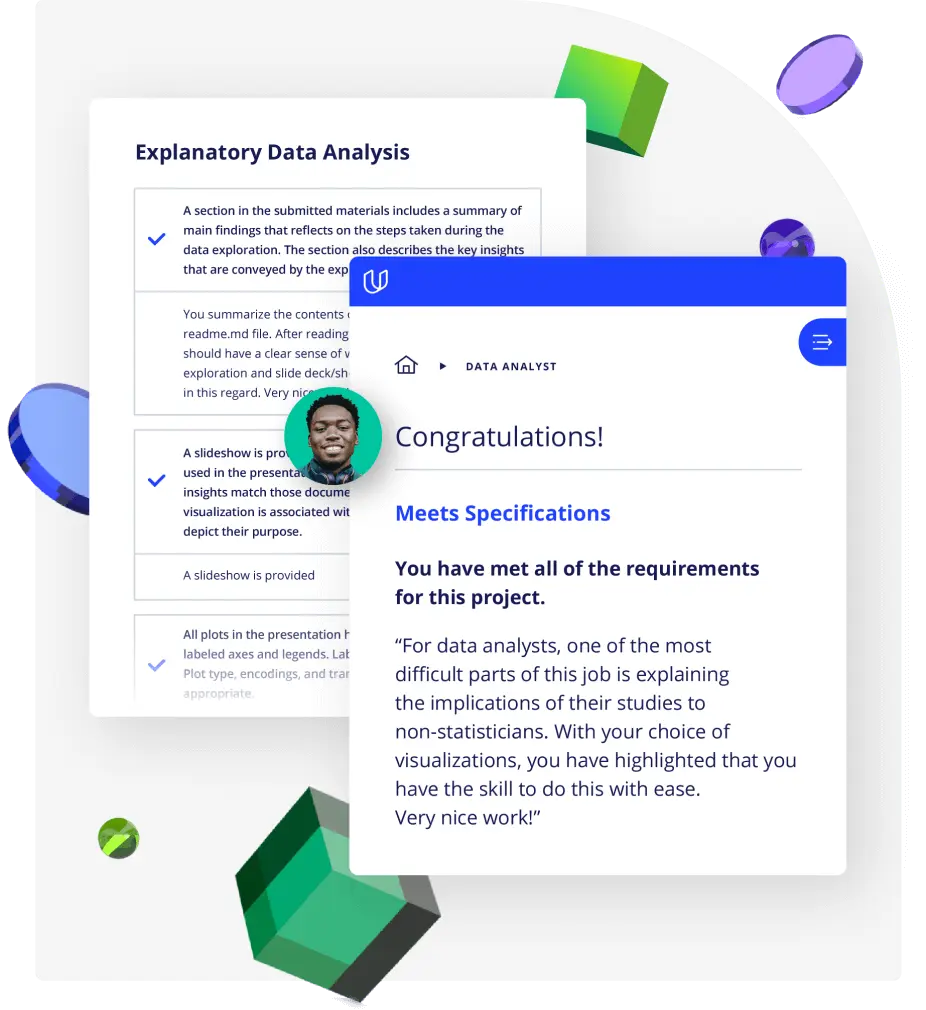
Demonstrate proficiency with practical projects
Projects are based on real-world scenarios and challenges, allowing you to apply the skills you learn to practical situations, while giving you real hands-on experience.
Gain proven experience
Retain knowledge longer
Apply new skills immediately
Top-tier services to ensure learner success
Reviewers provide timely and constructive feedback on your project submissions, highlighting areas of improvement and offering practical tips to enhance your work.
Get help from subject matter experts
Learn industry best practices
Gain valuable insights and improve your skills
Unlimited access to our top-rated courses
Real-world projects
Personalized project reviews
Program certificates
Proven career outcomes
Full Catalog Access
One subscription opens up this course and our entire catalog of projects and skills.
Average time to complete a Nanodegree program

Security Engineer